Reading Time: 8 minutes
With the advent of telecommunication technology, the attackers have also come up with an innovative strategy to fool users through fake phone calls. It utilises similar deceptive techniques of Phishing attack but since it is conducted mostly over the phone, it’s termed as ‘V-shing’, as in a shortened form of ‘Voice Phishing’. Reetwika, a cybersecurity consultant, cautions us against such attacks, in the weekly column, exclusively for Different Truths.
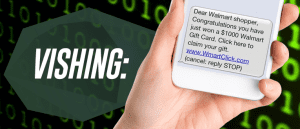
Have you heard of ‘Vishing Attack’ before? Well, it’s not a brand-new entry in the cybercrime world, rather like an old book sold in a new cover. With the advent of telecommunication technology, the attackers have also come up with an innovative strategy to fool users through fake phone calls. It utilises similar deceptive techniques of Phishing attack but since it is conducted mostly over the phone, it’s termed as ‘V-shing’, as in a shortened form of ‘Voice Phishing’.
Let us not get into the technical details of Phishing, instead look into some real-life Vishing incidents which shook the cyberspace recently. Even today, we trust more on a landline number than a call from an unknown mobile number. We feel a mobile number could be flying, but the landline is more reliable. Is that really so? That’s what is exploited by the attackers. Cannot a mobile number be masked to give a look of a landline number on your caller display?
Nowadays, more than 90% of cyber attacks and resulting data breaches begin with a Vishing attack. Nothing to get scared of, but it’s time to learn how to recognise and report such attacks so that you can safeguard yourself from the scammer at the right hour.
Tele Hypnosis
 Here’s a classic case of Vishing Attack. A lady doctor in the US was booked on charges of leaking critical health records of a reputed hospital where she was working as the RMO. Being one of the senior doctors, she apparently had privileged access to the patient database. Upon investigation, all alibis went against her as there were no trails of illegitimate admission to the database. The compromise happened using her official login credentials.
Here’s a classic case of Vishing Attack. A lady doctor in the US was booked on charges of leaking critical health records of a reputed hospital where she was working as the RMO. Being one of the senior doctors, she apparently had privileged access to the patient database. Upon investigation, all alibis went against her as there were no trails of illegitimate admission to the database. The compromise happened using her official login credentials.
Later when the case was handed over to the cyber cell, the real scam came out. Few days before the compromise happened, the lady doctor received three suspicious phone calls from one of her senior colleagues. He was a psychiatrist who hypnotised her over the telephone to commit the crime using her own database access credentials so that upfront it seems it was she who did it all, and the mastermind remained in the dark.
Shocker Emergency Calls
Wife of a New Delhi-based rich businessman got an emergency call which shattered her so badly that she agreed to give Rs. 50 lakhs cash to the attacker. It did not happen so simply though.
It was little after lunch when she received a call from her husband’s mobile who introduced himself as an eye-witness of her husband’s road accident. The spot was told to be quite far from their residence so that she could not arrive fast. Instead, as a goodwill gesture, she was offered by the so-called stranger to take her husband to the nearest hospital before it’s too late. He would need cash to start with the treatment as he was badly bleeding. If she was fine with the help, she can meet him directly at the hospital with the money.
Listening to such a pathetic news about a dear one, who would be able to keep nerves strong? And that’s exactly what the attacker took a chance on. She still tried to ring her husband’s other number, but it did not get through even after multiple tries. She was sure about his danger now. A sense of urgency had started running through her blood by then. She rushed to the designated hospital with a heavy volume of cash and handed it over to the attacker with the hope to proceed with the formalities ASAP without even meeting the patient. After three hours of shivering wait when she received a ring back from her husband from the same number, she was shaken.
Actually, the attacker had researched well about the businessman, his family members, his habits, his office timings, business meeting details from his online calendar, personal mobile number, etc., before launching the attack. And he was bang on. He chose a long business conference time to prank his family. Generally, during such formal meets, he used to keep his mobile in ‘meeting’ mode so that he is not disturbed by the incoming calls and messages. The attacker exploited this habit to drain off his battery by continuously calling to one of his numbers till the time the mobile got switched off. Meantime, the attacker forwarded the other number to an external device to fake the call. That was the reason why her calls did not connect and were eventually conned to believe the stranger’s words of panic.
Call from Police
This is one of the most shocking instances of Vishing. A reputed senior corporate received an automated voice message on his mobile which claimed to be a warning call from the central police station about his suspected involvement in a cybercrime. He was absolutely shocked to hear about such a preposterous blame which he could not relate to it in any way. The call ended with an option on IVRS saying that “If you think you have been wrongly booked, please dial 0 from the keypad and follow the instructions.” Who wouldn’t do that?
After a series of steps, he was finally said, “Thanks for your proactive support. Your charges are being waived off.” He kept down the phone happily. After a few days when real police walked into his office to arrest him, he was in deep shock.
What happened was, the first phone was a forged call. It was done via internet telephony using VoIP (Voice over Internet Protocol) technology through an IVRS (automated call) setup. It could be easily configured with no rocket science application. The steps he was asked to follow actually involved sharing of his username, password and network passkey which was later exploited by the attacker to send threatening emails to the Government from his official email ID. Apparently, all proofs were against him which led to the eventual arrest by real Police.
Claim Your Prize Money
This is as old and common as phishing emails. But nowadays, people are also getting these messages via text SMS or WhatsApp offers. Be sure to enter into any such deals after verifying the trustworthiness of the contest.
People have often been receiving lucrative business offers from overseas partners who are even ready to make the capital investments. You are only requested to share an account number to do business transactions. It used to happen over email earlier, now via chatting apps. Don’t get tricked by the conmen. Be alert before you make any such decision.
Save my Daughter
People often get calls or messages from unknown numbers who introduce themselves as NGO workers. They are contacting selected persons whom they believe to have big hearts who can make a difference to a needy’s life through small financial contributions.
“A poor farmer’s little daughter is suffering from the last stage of cancer, but he is unable to do treatment because of poverty. We are raising funds for the poor father if you could help.”
“Our little friends in Syria are in distress due to the extreme political conditions. If you can support us in raising funds, you will be blessed by Almighty. Click on this link to donate.”
“We are collecting relief to support the flood victims of Orissa. We are close to our target; a little contribution can help us achieving faster. Will you like to make a big difference through a small help?”
These are just a few examples. You will come across many if you start observing with a vigilant eye. From the above crime records what we could observe is in all the cases, there were some common strategies which were used to indulge victims to get conned easily like – automated voice calls, injecting a sense of urgency to make immediate decisions, unrealistic financial offers, force to claim huge prize money, impractical overseas business offers, emotional jerks, family emergency, help me messages, proactive security threats, early warning of consequences (heavy fines, deactivation, lawsuit etc), fake call from vigilance department etc.
Protect Yourself from the Vindictive Vishers
As I keep saying, cybercriminals mostly bank on common human psychology over the advanced use of technology. The best way to avert them is to stay alert and take appropriate actions at the right time. Here are few tips to identify and report Vishing attacks: –
Police or any legal authorities will never call you with an urgent notice if you are on their suspected list. It is bound to take place following a structured protocol. So, if anyone calls you impersonating as a law enforcement authority, immediately disconnect the phone and dial 100 to lodge a report against the calling number.
If you receive an emergency message on behalf of your near and dear ones when they are away, try to physically reach out to his last available location before handing over cash to any stranger. In the majority of the cases, it’s a prank. In case of road accidents, no cash deposits are required to be submitted to the hospitals for admission.
Do not share any personal confidential information like date of birth, Government IDs, bank account number, passwords, PINs etc over the phone, not even over automated IVRS calls.
Don’t trust your phone’s caller ID. Numbers can be masked to give a trusted guise as it can be easily forged using VoIP technology (internet telephony) to make the number appear more authentic.
After receiving any suspicious call from the bank, if you wish to verify if it was truly the case, do not dial from the same phone. The handset might have been already compromised such that even after you have dropped the call, it remains covertly active at the backend behind your knowledge. So that when you dial to the bank from the same handset and share your PIN, it gets recorded by the attacker on the covert call. Instead, use another device and SIM to dial the bank’s Customer Care number available on the backside of your debit or credit card.
Try to gauge if the caller is speaking fluently in your language or does it sound robotic. With a text to speech synthesizer, voice can be easily automated to create an audio message. Or the attacker could be just reading out a text written in different lingo, without knowing the language you speak.
Try to check if the caller is greeting you with your name or just addressing you blankly during the opening conversation. In case of vishing, the calls are randomly done on a mass scale without knowing the recipient’s identity.
 Do not click on any hyperlink at the direction of an unidentified caller or text messages from an unsolicited sender. It might be a fake website created to capture your confidential information. In case you need to visit an unfamiliar website for legitimate verification purposes, be sure to confirm if the link is genuine. Just follow my simple tip – Type in any random username and password for signing in, if they are accepted it’s a fake site because the backend server does not recognize the correct combination of keys; if the access is rejected then it’s likely to be a trusted one.
Do not click on any hyperlink at the direction of an unidentified caller or text messages from an unsolicited sender. It might be a fake website created to capture your confidential information. In case you need to visit an unfamiliar website for legitimate verification purposes, be sure to confirm if the link is genuine. Just follow my simple tip – Type in any random username and password for signing in, if they are accepted it’s a fake site because the backend server does not recognize the correct combination of keys; if the access is rejected then it’s likely to be a trusted one.
From surprising voice messages, do not ring back to any unverified Toll-Free number if you are not sure about its legitimateness. It might be a trap to collect your ATM or Telebanking PINs through a series of automated keypunching steps. Also never keep such calls on hold to verify the caller ID. They can still hack into your network to steal your credentials.
Be careful not to enter any personal conversations while you have been put on ‘hold’ by the tele-caller. You cannot hear him but he could still listen to you as you are not on mute. At times, it is purposely done by some malicious agencies to sniff consumer data.
Last but not the least, get yourself registered to the ‘National Do Not Call Registry’. That reduces the risk of Vishing to a significant extent. Caller identity will be masked in the telephone registry before saving. So, even if it is leaked, the vishers cannot do much with a half-displayed contact number.
©Reetwika Banerjee
Photos from the Internet
#Vishing #ATM #CallerID #SuspiciousCalls #HowToHandleSuspiciousCalls #ProtectAgainstVishing #CyberCrimeOnPhone #CyberCrime #WaysToProtectYourIdentity #DifferentTruths




















